
Security Risk Assessment Explained: Cut Theft by 30% in 2026
Share
Properties conducting thorough security risk assessments reduce theft incidents by nearly 30% within the first year. Yet many home and business owners misunderstand what these assessments truly involve, often confusing them with simple equipment installations. This guide clarifies how to perform effective security risk assessments and apply findings to maximize protection, combining physical barriers, technology, and procedural controls into a cohesive defense strategy.
Table of Contents
- What Is A Security Risk Assessment And Why It Matters
- Step-by-Step Process For Conducting A Security Risk Assessment
- Common Misconceptions And Mistakes In Security Risk Assessments
- Frameworks And Models To Organize Security Risk Assessments
- Applying The Assessment: Choosing The Right Security Solutions
- Reviewing And Updating Your Security Risk Assessment
- Enhance Your Security With Our Expert Solutions
- Frequently Asked Questions
Key Takeaways
| Point | Details |
|---|---|
| Security risk assessments identify vulnerabilities | Properties conducting assessments reduce theft by nearly one-third in just one year. |
| Effective assessments evaluate multiple risk layers | Analysis includes physical security, procedural gaps, and behavioral vulnerabilities beyond technology alone. |
| Frameworks like NIST improve execution | Structured frameworks boost assessment clarity and execution by 40%, organizing complex tasks. |
| Regular updates prevent outdated security postures | Annual or biennial reassessment catches evolving threats and changing property conditions. |
| Matching solutions to prioritized risks maximizes protection | Targeted controls aligned with identified risks ensure efficient resource use and enhanced security. |
What Is a Security Risk Assessment and Why It Matters
A security risk assessment is a systematic evaluation identifying vulnerabilities, threats, and weaknesses in your property’s protection. For U.S. home and business owners, these assessments pinpoint where theft, vandalism, fire, or unauthorized access could occur, creating actionable roadmaps to strengthen defenses. Unlike simply installing cameras or alarms, assessments analyze the complete security landscape.
Properties conducting security risk assessments reduce theft by nearly one-third in just one year. This dramatic impact stems from addressing root causes rather than symptoms. Assessments reveal gaps in physical barriers, procedural weaknesses like unmonitored entry points, and behavioral risks such as inconsistent door locking.
Security risk assessments typically evaluate three vulnerability categories:
- Physical vulnerabilities: Weak locks, inadequate lighting, accessible windows, or poorly placed valuables
- Procedural vulnerabilities: Missing protocols for key control, alarm verification, or visitor management
- Behavioral vulnerabilities: Employee or resident habits that compromise security, like propping doors open
Understanding security safe basics helps illustrate how physical controls fit into broader risk mitigation strategies. Assessments matter more than equipment alone because they ensure every security measure addresses an identified threat. You avoid wasting money on unnecessary technology while missing critical gaps.
“A comprehensive security risk assessment transforms reactive property protection into proactive threat prevention, reducing both incident frequency and severity.”
The assessment process evaluates existing controls before recommending improvements, ensuring new investments complement rather than duplicate protections. This approach explains why investing in high security solutions delivers measurable returns when guided by assessment findings. Properties with formal assessments experience fewer false alarms, lower insurance premiums, and faster incident response.
For businesses, assessments protect revenue-generating assets, customer data, and employee safety. For homeowners, they safeguard irreplaceable valuables, family members, and peace of mind. The NIST Risk Management Framework provides standardized methods that property owners can adapt to their specific contexts.

Step-by-Step Process for Conducting a Security Risk Assessment
Executing a thorough security risk assessment follows five core steps that transform vague concerns into concrete action plans. This systematic approach ensures you identify genuine threats rather than imagined risks.
-
Identify and classify critical assets: List everything requiring protection, from jewelry and documents to inventory and equipment. Categorize by value and replacement difficulty. Include both tangible items and intangible assets like privacy and safety.
-
Analyze potential threats: Examine threats from natural disasters, human actors like burglars or vandals, and technical failures such as alarm malfunctions. Consider historical crime data for your area and property-specific factors like visibility from streets.
-
Identify vulnerabilities: A systematic assessment process improves risk identification and control selection. Walk your property noting weak points: unlocked gates, dim entryways, windows without sensors, or missing policies for key distribution.
-
Estimate likelihood and impact: Assign probability ratings to each threat-vulnerability combination. A ground-floor window facing an alley has higher break-in likelihood than a second-floor window visible from the street. Evaluate potential damage if incidents occur.
-
Evaluate existing controls: Document current protections before recommending additions. You might already have motion sensors covering some vulnerable areas, allowing budget reallocation to unprotected zones.
Pro Tip: Use a simple risk matrix plotting likelihood against impact. Focus resources on high-likelihood, high-impact risks first, then address lower-priority items as budget allows.
When choosing safes for asset protection, your assessment findings should guide fire rating, burglary resistance, and size requirements. Understanding the role of security systems helps you layer technological controls with physical barriers.
| Assessment Step | Key Questions | Common Outputs |
|---|---|---|
| Asset Identification | What needs protection? What is replacement cost? | Prioritized asset inventory with valuations |
| Threat Analysis | Who or what could cause harm? What is historical precedent? | Threat profiles ranked by likelihood |
| Vulnerability Identification | Where are security gaps? What procedures are missing? | Vulnerability map with severity ratings |
| Risk Estimation | Which combinations pose greatest danger? | Risk matrix prioritizing mitigation targets |
| Control Evaluation | What protections already exist? Where are coverage gaps? | Current security baseline and gap analysis |
Effective protection strategies emerge from methodical assessment rather than reactive purchases. Documentation throughout the process creates accountability and tracks security improvements over time.
Common Misconceptions and Mistakes in Security Risk Assessments
Many property owners undermine their assessments through predictable errors that reduce effectiveness and waste resources. Recognizing these pitfalls prevents costly mistakes.
The most damaging misconception treats assessments as purely technology exercises. Installing cameras and alarms addresses only one risk dimension. Procedural gaps like uncontrolled key distribution or behavioral issues like employees disabling sensors to avoid false alarms create vulnerabilities no camera can fix. Comprehensive assessments examine human factors alongside hardware.
Forty percent of small businesses fail to update risk assessments annually, missing evolving threats. Security environments change constantly. New neighbors, altered traffic patterns, updated crime trends, renovated entry points, or added inventory all shift your risk profile. Static assessments become obsolete quickly.
Common assessment mistakes include:
- Focusing exclusively on external threats: Insider risks from employees, contractors, or residents often account for significant incidents but receive minimal attention
- Ignoring natural disaster risks: Fire, flooding, or severe weather can damage property and assets as severely as theft
- Overestimating technology effectiveness: Cameras deter some criminals but do nothing without monitoring, maintenance, and response protocols
- Underestimating procedural controls: Clear policies for access management, alarm response, and emergency procedures often prevent more incidents than expensive equipment
- Failing to test controls: Assumptions about alarm functionality or camera coverage break down without regular testing and drills
Pro Tip: Involve multiple perspectives in your assessment. Property occupants, neighbors, and professional consultants each notice different vulnerabilities based on their vantage points and experience.
Understanding why security integration matters prevents the mistake of treating each security element as isolated rather than part of a coordinated system. Cameras become more effective when integrated with motion sensors and alarms, creating layered detection.
Another frequent error involves conducting assessments during convenient times rather than high-risk periods. Evaluating security at midday Monday misses vulnerabilities apparent during weekend evenings or holiday closures when properties sit empty. Schedule assessment activities to match actual occupancy patterns.
Frameworks and Models to Organize Security Risk Assessments
Frameworks like NIST Risk Management improve assessment clarity and execution by 40% by providing structured approaches that prevent oversight and organize complex tasks. Rather than ad hoc evaluations, frameworks create repeatable processes producing consistent results.
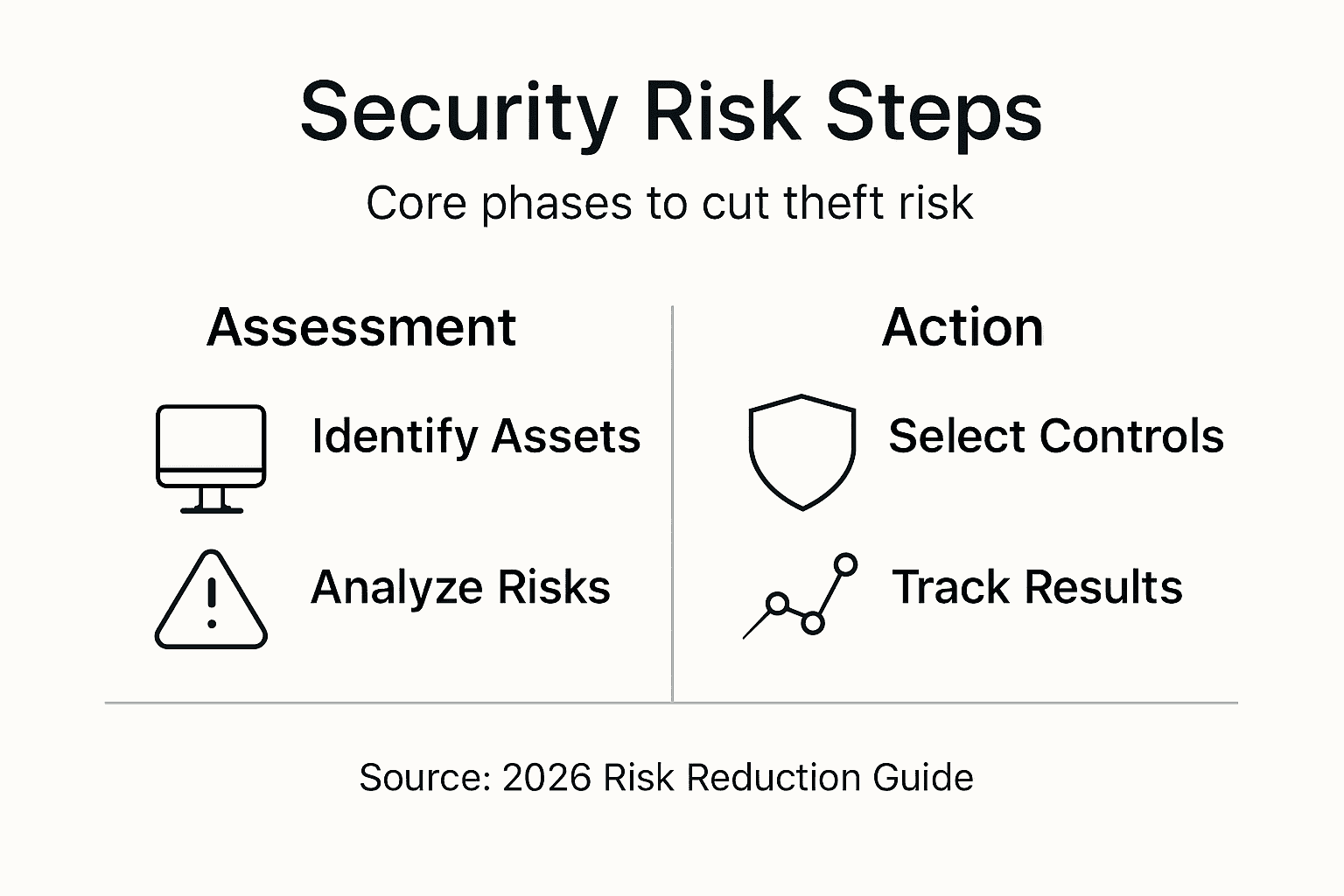
The cyclical assessment framework follows six phases:
- Asset Identification: Catalog everything requiring protection with replacement costs and criticality ratings
- Threat Analysis: Identify potential harm sources from criminals, natural events, technical failures, or insider actions
- Vulnerability Evaluation: Map weaknesses in physical barriers, technological controls, procedures, and behaviors
- Risk Prioritization: Rank threats by likelihood and potential impact, focusing resources on greatest dangers
- Control Implementation: Deploy security measures matched to prioritized risks and available budgets
- Review and Update: Reassess periodically to catch new threats, verify control effectiveness, and adapt to property changes
This cycle repeats annually or when significant property modifications occur, maintaining current protection. The framework prevents common mistakes like implementing controls before understanding threats or neglecting follow-up verification.
“Structured assessment frameworks transform overwhelming security decisions into manageable steps with clear objectives and measurable outcomes.”
| Approach | Asset Coverage | Threat Analysis | Control Selection | Maintenance | Typical Outcome |
|---|---|---|---|---|---|
| Unstructured | Incomplete, focuses on obvious items | Reactive to recent incidents | Random, driven by sales pitches | Irregular, crisis-driven | Gaps remain, wasted spending |
| Framework-Based | Comprehensive inventory | Proactive, data-informed | Targeted to prioritized risks | Scheduled reassessment | Efficient resource use, reduced incidents |
Frameworks also improve communication when working with security professionals or insurance providers. Standardized terminology and processes help everyone understand current protections and recommended improvements. Following asset protection workflows ensures systematic coverage without redundant efforts.
The NIST Risk Management Framework offers detailed guidance adaptable to properties of any size. While originally designed for information security, its principles apply equally to physical security contexts. Smaller properties can simplify framework steps while maintaining the core logic.
Adopting a framework does not require expensive consultants or software. Simple spreadsheets tracking assets, threats, vulnerabilities, and controls provide sufficient structure for most home and small business assessments. The key benefit comes from systematic thinking rather than sophisticated tools.
Applying the Assessment: Choosing the Right Security Solutions
Translating assessment findings into effective security measures requires matching solutions to identified risk levels and contexts. Matching solutions to prioritized risks ensures efficient resource use and enhanced protection rather than generic installations.
Effective security combines three control categories:
- Physical barriers: Locks, safes, reinforced doors, window bars, and lighting that prevent or delay unauthorized access
- Technological controls: Cameras, motion sensors, alarms, and access control systems that detect and document incidents
- Procedural controls: Policies, training, and protocols governing key management, visitor screening, and emergency response
Balance among categories matters more than expensive equipment in any single area. A business with cutting-edge cameras but no key control policy remains vulnerable to insider theft. A home with excellent locks but no alarm system lacks detection when barriers fail.
Pro Tip: Prioritize controls offering multiple benefits. Motion-activated lighting deters criminals while improving navigation safety. Fire-resistant safes protect against both theft and natural disasters.
Consider two scenarios demonstrating targeted solutions:
Scenario 1: An urban retail business faces high shoplifting risk but low burglary threat due to constant foot traffic. The assessment prioritizes visible deterrents like security cameras monitoring customer areas, employee training on theft indicators, and point-of-sale auditing procedures. Heavy safes protect cash during business hours.
Scenario 2: A suburban home in a low-crime area prioritizes fire protection for irreplaceable documents and jewelry over burglary deterrence. The assessment emphasizes fire-resistant safes, smoke detectors, and emergency evacuation procedures. Basic door locks and window sensors provide adequate perimeter security without extensive camera systems.
| Solution Category | Primary Benefits | Typical Limitations | Best Applications |
|---|---|---|---|
| Physical Barriers | Prevent access, require no power, low maintenance | Cannot detect or document incidents alone | High-value asset storage, perimeter hardening |
| Technology Systems | Detection, documentation, remote monitoring | Require power and maintenance, generate false alarms | Large properties, unoccupied periods, evidence collection |
| Procedural Controls | Address human factors, cost-effective, adaptable | Depend on compliance, require training | Organizations with employees, high-traffic properties |
Exploring security solutions for urban environments illustrates how context shapes appropriate controls. Apartment dwellers face different threats than suburban homeowners, requiring distinct security emphases.
Cost-benefit analysis guides investment decisions. Calculate each risk’s potential loss, multiply by likelihood, and compare to control costs. Spending $2,000 to prevent a $50,000 loss with 10% annual probability delivers clear value. Spending $5,000 to prevent a $1,000 loss with 1% probability wastes resources better allocated elsewhere.
Reviewing and Updating Your Security Risk Assessment
Annual or biennial reassessment helps avoid outdated security postures and reduces incident risk by catching emerging threats and changing property conditions. Static assessments create dangerous false confidence as environments evolve.
Schedule reassessments based on property characteristics:
- High-risk environments: Annually for businesses in urban areas, properties storing valuable inventory, or locations with recent crime increases
- Moderate-risk environments: Every 18-24 months for suburban homes, low-traffic businesses, or properties with stable surroundings
- After significant changes: Following renovations, occupancy changes, nearby development, or security incidents regardless of scheduled timing
Reassessment focuses on changes since the last evaluation rather than repeating the entire process. Review asset inventory for additions or removals. Update threat analysis with recent crime data or new vulnerabilities from property modifications. Verify existing controls remain functional through testing and maintenance records.
Documentation tracks security improvements and justifies ongoing investments. Maintain records showing:
- Initial assessment findings and risk priorities
- Implemented controls with installation dates and costs
- Incident history noting what occurred and controls involved
- Reassessment dates and updated findings
- Planned improvements with target completion dates
This documentation supports insurance claims, provides accountability for security budgets, and helps identify patterns requiring attention. Properties demonstrating regular reassessment often qualify for insurance discounts reflecting reduced risk profiles.
Learning to maintain security systems ensures reassessments reveal actual rather than assumed protection levels. Cameras with dead batteries or alarms with disabled zones create gaps invisible without testing.
Reassessment also evaluates whether implemented controls achieved expected results. Did camera installation reduce incidents in targeted areas? Are procedural changes being followed consistently? Measuring outcomes validates security investments and guides future decisions.
Enhance Your Security with Our Expert Solutions
Now that you understand comprehensive security risk assessment, explore our curated selection of professional-grade protection products designed to address your identified vulnerabilities. Whether your assessment revealed gaps in surveillance coverage, asset storage, or perimeter security, we offer solutions engineered for reliability and effectiveness.
Our live security cameras provide remote monitoring capabilities that turn detection into actionable response. Compare types of security cameras to match your specific risk profile and property layout. Discover proven security solutions tailored to your environment, backed by professional specifications and expert guidance. Transform your assessment findings into measurable protection improvements with equipment trusted by security professionals and property owners nationwide.
Frequently Asked Questions
How often should I perform a security risk assessment?
Conduct full assessments annually for high-risk properties or businesses, and every 18-24 months for moderate-risk homes. Immediate reassessment is essential after significant property changes, nearby crime increases, security incidents, or renovations that alter access points or vulnerabilities.
Can I conduct a security risk assessment myself or should I hire a professional?
Most home and small business owners can perform effective assessments using structured frameworks and checklists. Consider professional consultants for complex properties, high-value assets, regulatory compliance requirements, or when you lack confidence identifying vulnerabilities. Professionals bring experience spotting non-obvious weaknesses.
What are the most common security risks that assessments uncover?
Assessments frequently reveal inadequate lighting near entry points, missing or outdated locks, unmonitored access points, lack of procedures for key control, inconsistent alarm use, poor camera placement with blind spots, and behavioral issues like propped doors. Procedural gaps often outnumber physical vulnerabilities.
How do I know if my current security solutions adequately address identified risks?
Test existing controls through simulations, review incident logs for patterns indicating failures, verify technology functions properly through regular maintenance, and compare your protection layers against prioritized risk levels. Gaps where high-priority risks lack corresponding controls indicate inadequate coverage requiring upgrades.
What is the difference between physical security and procedural controls in risk assessments?
Physical security includes tangible barriers and equipment like locks, safes, cameras, and reinforced doors that prevent or detect unauthorized access. Procedural controls are policies and practices governing security equipment use, access management, key distribution, visitor screening, and emergency response. Both categories must work together for comprehensive protection.
Recommended
- Business Security Needs: Protecting Assets in 2026 – Safes and Security Direct
- Smart Home Security: Cut Insurance 15% & Boost Safety – Safes and Security Direct
- Asset Protection Strategies 2026: Safeguard Your Business Assets – Safes and Security Direct
- Role of Commercial Security: 50% Crime Reduction Proven – Safes and Security Direct
