
Security audit guide: meaning, steps, and property protection
Share
A security audit is one of the most misunderstood tools in asset protection. Many organizations wrongly believe that passing an audit eliminates all vulnerabilities and guarantees safety. It doesn’t. What a security audit actually does is give you a clear, structured picture of where your defenses hold up and where they fall short. For businesses and property managers, that picture is invaluable. This guide breaks down what a security audit truly means, how the process works step by step, and how you can use audit findings to build stronger, more resilient protection for your assets and people.
Table of Contents
- What is a security audit?
- The five phases of a modern security audit
- Security audits for property management: Physical and operational focus
- Internal vs external audits and common misconceptions
- Frequency, costs, and future trends in security auditing
- Why security audits matter more than ever: An expert perspective
- How Safes and Security Direct can help with your security audits
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Security audit meaning | A security audit checks how well your policies and controls protect assets and meet standards. |
| Five audit phases | Every audit has scoping, evidence collection, control testing, analysis, and reporting steps. |
| Physical security focus | Property managers must audit sites, access, and training to close security gaps. |
| Certification vs. safety | An audit certificate proves compliance, but ongoing attention is needed for true protection. |
| Audit cost and trends | Audits are more frequent and costly than many expect, but automation and planning can cut both. |
What is a security audit?
Let’s cut through the jargon first. A security audit is a systematic, independent, and documented examination of an organization’s information security management system, policies, processes, and controls. That’s the formal definition, but in practice it means someone is taking a hard, structured look at everything you have in place to protect your assets and asking: does this actually work?
For property managers and business owners, security audits come in two main flavors. Information security audits focus on digital systems, data handling, network access, and software controls. Physical security audits examine your site layout, access points, surveillance systems, locks, lighting, and staff procedures. Most organizations need both, and the best audits treat them as interconnected rather than separate concerns.
Understanding the security standards definition that underpin audits helps you set realistic expectations. Audits typically align with recognized frameworks to ensure consistency and credibility.
| Framework | Primary focus | Common use case |
|---|---|---|
| ISO 27001 | Information security management | Enterprise and regulated industries |
| NIST CSF | Cybersecurity risk management | Government and critical infrastructure |
| SOC 2 | Service organization controls | Cloud and SaaS providers |
| Physical security standards | Site and access controls | Property and facilities management |
The role of security standards in audit design is significant. Core audit mechanics align with frameworks like ISO 27001 and NIST, giving auditors a consistent benchmark to measure your controls against. Without a framework, an audit is just an opinion.
“A security audit doesn’t tell you that you’re safe. It tells you where you stand relative to a defined standard. That distinction changes everything about how you act on the results.”
What audits reveal most clearly are gaps: missing policies, untested controls, outdated procedures, and overlooked physical vulnerabilities. That’s the real value. Not a certificate on the wall, but a roadmap for improvement.
The five phases of a modern security audit
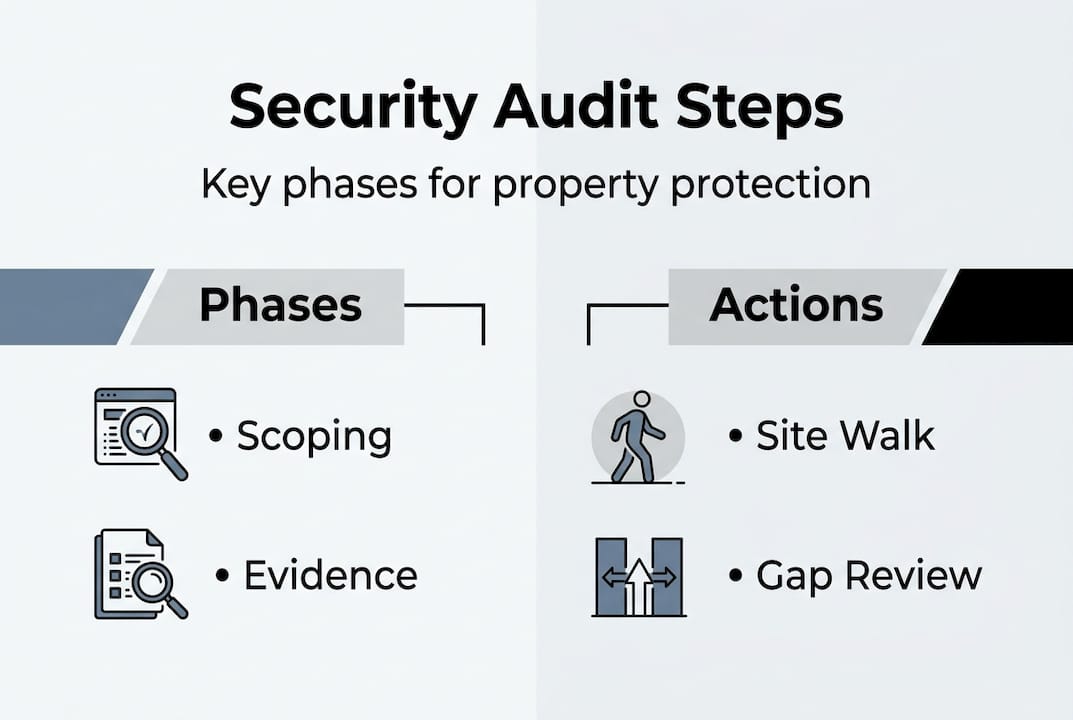
With the definition and standards established, the logical next question is how a security audit actually works step by step. Security audits follow a five-phase process: scoping, evidence collection, control testing, analysis, and reporting with remediation. Each phase builds on the last, and skipping or rushing any one of them weakens the entire effort.
- Scoping and planning. Define what’s being audited, which systems, sites, or processes are in scope, and what standards apply. Poor scoping is the single biggest reason audits fail to deliver useful results.
- Evidence collection. Auditors gather documentation, interview staff, review access logs, and inspect physical controls. The quality of evidence directly determines the quality of findings.
- Control testing. Each control is tested against the standard. This might mean attempting unauthorized access, reviewing camera footage retention, or checking whether fire-resistant safes meet rated standards.
- Analysis and findings. Auditors assess gaps, rate risk levels, and identify root causes. This is where patterns emerge that point to systemic issues rather than isolated problems.
- Reporting and remediation. A formal report documents findings, assigns risk ratings, and recommends corrective actions. The audit benefits only materialize if you act on this report.
Pro Tip: Invest the most time in scoping. A narrow or vague scope produces findings that don’t reflect your real risk exposure. Push for a scope that covers all critical assets, not just the ones that are easy to assess.
For property managers, each phase maps to practical actions. Scoping means listing every entry point and system. Evidence collection means pulling access logs and maintenance records. Control testing means physically checking locks, cameras, and alarm responses. Use an asset protection checklist to make sure nothing gets missed during the evidence and testing phases.
| Audit phase | ISO 27001 alignment | Practical property action |
|---|---|---|
| Scoping | Clause 4: Context of organization | Map all assets and entry points |
| Evidence collection | Clause 9: Performance evaluation | Pull access logs and maintenance records |
| Control testing | Clause 6: Planning | Test locks, cameras, and alarm systems |
| Analysis | Clause 10: Improvement | Rate gaps by risk level |
| Reporting | Annex A controls | Issue remediation plan with deadlines |
Security audits for property management: Physical and operational focus
Knowing how audits are structured, it’s vital to see how these concepts play out in the physical landscape of property management. Physical security audits are not just about technology. They cover site surveys, perimeter checks, access controls, surveillance, and staff training in a coordinated way that digital-only audits miss entirely.
Here’s how a physical security audit typically unfolds for a property or commercial site:
- Build your audit team. Include a mix of internal staff and an independent reviewer to avoid blind spots.
- Define the scope. Identify every building, zone, access point, and system that needs assessment.
- Conduct a facility inspection. Walk every perimeter, check lighting, fencing, gates, and signage.
- Audit your systems. Test cameras, alarms, intercoms, and access control hardware for function and coverage gaps.
- Identify risks. Document every vulnerability found, from broken locks to camera blind spots to untrained staff.
- Build an action plan. Prioritize fixes by risk level and assign clear ownership and deadlines.
One statistic stands out in access control assessments: 34% of access control reviews reveal critical failures, making it the single highest-risk area in most physical audits. Tailgating, shared credentials, and outdated key management are the most common culprits.

Pro Tip: Technology alone won’t close your security gaps. Pair camera systems and access controls with written policies and regular staff training. A camera that nobody monitors and a policy that nobody follows are both useless.
For asset protection methods to work at the property level, the audit must connect physical findings to operational procedures. Reviewing commercial security tips alongside your audit findings helps you prioritize the right fixes first.
Internal vs external audits and common misconceptions
Beyond the how, it’s crucial to understand the types of audits you may encounter and the limitations and misconceptions associated with each.
Internal audits are self-assessments; external audits are conducted by third parties and are often certifying. Certification shows conformance with a standard but does not eliminate vulnerabilities. That distinction matters enormously for how you interpret results.
Organizations audit for several distinct reasons:
- Compliance-driven: Required by regulation, contract, or industry standard.
- Insurance-driven: Insurers increasingly require audit evidence before issuing or renewing coverage.
- Policy-driven: Internal governance requires regular review of security controls.
- Risk-driven: Leadership wants an independent view of exposure before making investment decisions.
The most persistent misconception is that achieving certification means you are secure. It means you were conformant with a standard at a specific point in time. Security environments change constantly. New staff join, systems get updated, and threat landscapes shift. A point-in-time audit captures a snapshot, not a live feed.
“Certification is the beginning of a security program, not the end. Organizations that treat it as a finish line are the ones that get surprised.”
Continuous monitoring fills the gap between audits. Automated tools, regular internal reviews, and real-time alerting keep your security best practices current between formal audit cycles. Checking compliance benchmarks helps you understand how your audit frequency and rigor compare to peers in your sector.
Frequency, costs, and future trends in security auditing
Having established the practicalities and realities of different audit types, we’ll now clarify how often audits happen, what they cost, and what’s next.
97% of organizations conduct at least two audits annually, and startups underestimate costs by 2.4 times on average. That cost gap catches many smaller businesses off guard when they first engage an external auditor.
| Audit type | Typical frequency | Average duration | Cost range |
|---|---|---|---|
| Internal audit | Quarterly or biannual | 2 to 4 weeks | Low (staff time) |
| External compliance audit | Annual or biannual | 4 to 6 months | $15,000 to $100,000+ |
| Physical security assessment | Annual | 1 to 3 weeks | $5,000 to $30,000 |
| Continuous monitoring | Ongoing | Real time | Subscription based |
Key cost drivers include:
- Organization size and complexity. More sites, systems, and staff mean more audit hours.
- Scope breadth. Audits covering both physical and information security cost more than single-focus reviews.
- Internal vs external. External auditors charge for expertise and independence.
- Automation adoption. Automation reduces audit time by up to 40% and improves consistency, which lowers long-term costs significantly.
The trend toward automated evidence collection and continuous control monitoring is reshaping how organizations approach the audit process. Instead of scrambling to gather evidence once a year, leading organizations maintain audit-ready documentation year-round. For property managers, this means digital access logs, automated camera health checks, and real-time alarm monitoring feeding into a central dashboard.
If you’re planning your audit budget for 2026, start by reviewing how you prioritize security solutions across your portfolio. Automation investments that reduce audit preparation time often pay for themselves within two audit cycles.
Why security audits matter more than ever: An expert perspective
Here’s the uncomfortable truth most audit guides won’t tell you: the process itself is not the hard part. Acting on what the audit reveals is where most organizations fail.
We see this pattern consistently. A business completes a thorough audit, receives a detailed report with clear recommendations, and then files it away while daily operations take over. Six months later, the same vulnerabilities are still open. The audit didn’t fail. The follow-through did.
Access controls and staff training surface as high-impact gaps in nearly every physical security audit we encounter. These aren’t glamorous fixes. They don’t involve buying new technology. They require changing how people behave and how management enforces policy. That’s harder than installing a camera.
The most effective organizations treat audit findings as a management accountability tool, not just a technical checklist. When a gap in essential security tips is identified, someone owns it, has a deadline, and reports back on resolution.
Pro Tip: If you only act on one section of your audit report, make it access controls and security culture. Those two areas consistently deliver the highest return on remediation effort.
Audits are only as valuable as the culture that receives them. Build a team that sees findings as opportunities, not criticism, and your audit program will actually improve security rather than just document it.
How Safes and Security Direct can help with your security audits
Putting audit principles into real action requires reliable tools, expert guidance, and the right equipment to close the gaps your audit uncovers.
Safes and Security Direct offers a full range of professional-grade security products designed to address the physical vulnerabilities that audits most commonly expose. From advanced surveillance cameras and access control systems to fire-resistant and burglary-resistant safes, the product catalog maps directly to the action items that come out of a physical security audit. You can also explore the security audit resource library for guidance on audit planning, standards review, and equipment recommendations tailored to your site’s specific needs. Reach out directly for support on staff training resources or to get matched with the right solutions for your next audit cycle.
Frequently asked questions
What exactly does a security audit cover?
A security audit examines your policies, physical and digital controls, staff actions, and procedures to spot vulnerabilities and confirm compliance with standards like ISO 27001. It covers both your information security management system and physical site controls depending on the audit scope.
How often should you schedule a security audit?
97% of organizations conduct at least two audits per year, with regulated industries and larger enterprises often scheduling them quarterly. Your frequency should match your risk exposure and any contractual or regulatory requirements.
Is passing a security audit enough to guarantee safety?
No. Passing an audit demonstrates conformance with a standard at a point in time, but ongoing vigilance, staff training, and continuous monitoring are what sustain real asset security between audit cycles.
What is the typical cost and duration of a security audit?
External compliance audits average around five months in duration, and startups underestimate costs by 2.4 times on average. Physical security assessments tend to be shorter and less expensive, but scope and organization size drive costs significantly in both cases.
Recommended
- Why use security audits to protect your property – Safes and Security Direct
- Industry Security Best Practices: Protect Property and Reduce Risk – Safes and Security Direct
- How to secure property effectively: A practical guide – Safes and Security Direct
- Asset Protection Workflow Guide for Maximum Security – Safes and Security Direct
